
Comprehensive and meant for beginners and intermediate security testers/pen testers.
Expert-designed extensive course for those who want to get started in Security Testing.
Receive Q&A support, Educator access, masterclasses, and much more. Enrol now!
Access this and 27 other courses along with AI Masterclasses, 1-1 Mentoring, and more.
Join Finer Circle / Year
Access this and 27 other courses along with AI Masterclasses, 1-1 Mentoring, and more.
Join Finer Circle / YearGet comfortable with Security Testing in a few hours
Basics of cybersecurity
Fundamentals of Linux Operating System
Network security basics
OWASP
Various tools used in security testing
Web Application Penetration Testing
A Decade of experience diluted into a few hours!
Master Security Testing with no experience
Access to an industry expert Educator
Learn at your own pace - receive lifetime access
Familiarize yourself with Burp Suite





Saurabh, a cyber security pro for almost a decade, excels in precise penetration testing and adept vulnerability assessment. He seamlessly implements tools like Qualys and Crowdstrike, while his mastery extends to innovative solutions like AttackIQ. Beyond tech, Saurabh navigates cyber regulations with finesse, proudly holding a CISA certification.

This is a place where I got my concepts clear and I suggest people can choose this course can understand the basics in a better way I thank The Test Tribe for the course.

...He is the only person you require if you want guidance for any role in Testing. Thank you for teaching and sharing your experience.

The trainer was excellent and I gained valuable insights and practical experience...

...Kudos for his insightful teaching and visualization techniques!

His course is awesome. If you are keen in learning, go ahead with it.
You have no prior experience in pentesting
You want to start your career in security testing
You want to learn Burp Suite and other tools
You want an Expert Educator
You want to learn affordably
You want to learn at your own pace
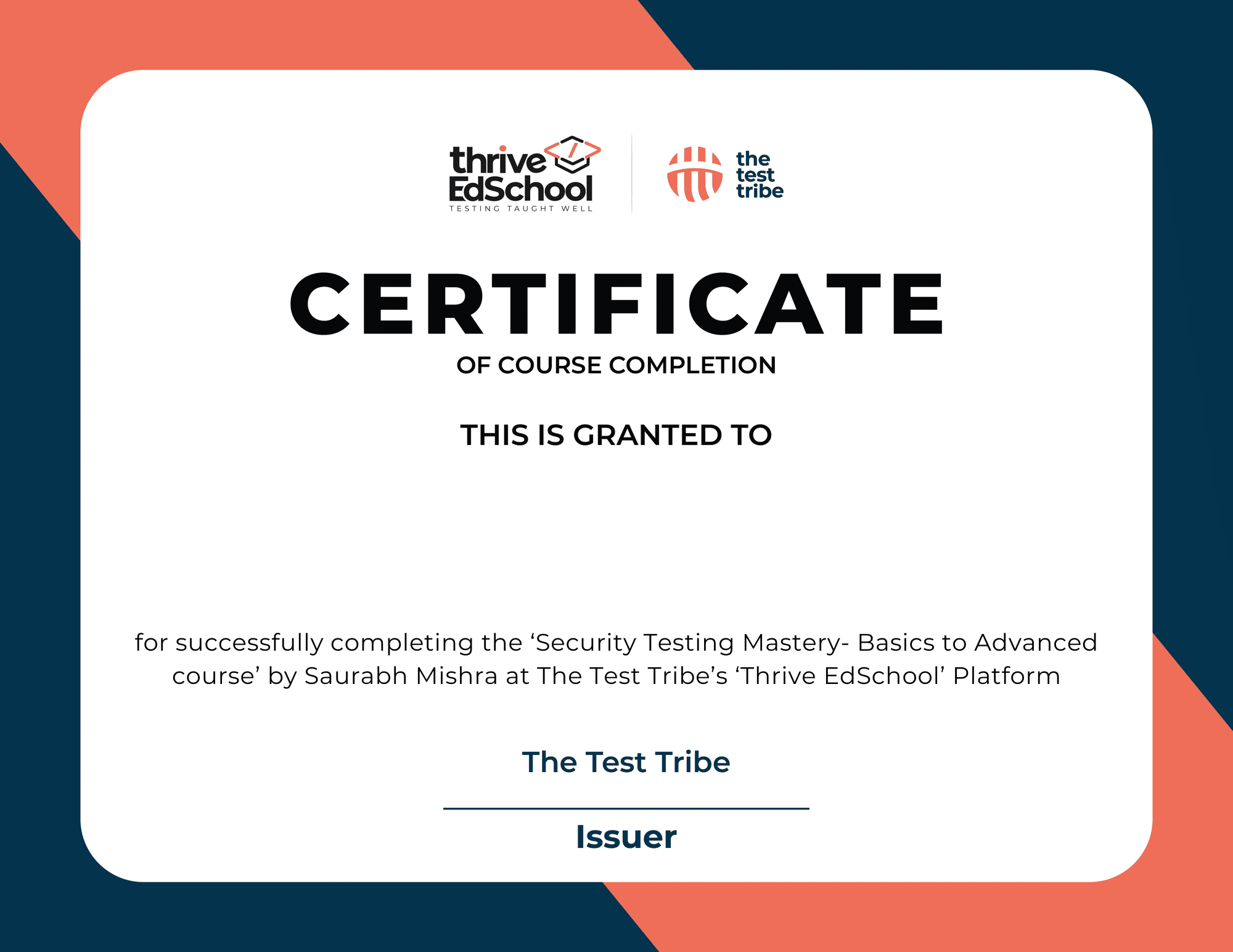
We’re glad to offer you a certificate of completion for our Security Testing Mastery course as a proof of your commitment to learning.
Everything you need to know about this course.
Still can’t find what you were looking for?
Chat with us using the Chat Bot.
Individuals interested in initiating their careers in security testing with no prior experience or those seeking a refresher in security testing using Burp Suite.
This course is updated as of 2023.
Yes, you will be provided with a certificate upon completion of the course.
Yes! You will receive lifetime access to the course.
Once you complete the course, you can email us at [email protected]. For you to be eligible for a feesback, the course should be complete within 15 days of purchase. Note that, you will no longer have the access to the course once the fees back is claimed.
Yes! No prior programming or automation experience is required for you to begin this course.
PEOPLE’S POPULAR CHOICE
Career Maker
Beyond Selenium


Must know skill

Projects Included

Expert Educator

Bestseller

Bestseller

Newly Launched

Newly Launched
Newly Launched


Newly Launched
Must know skill

Newly Launched

Master Programming
Must know skill

Master Programming

Career Transition


Beyond JMeter

Projects Included

Beyond Selenium

Projects Included


Master basics

Highest Rated


Join our community of testers and start your journey